Simulation of hardware design. The collection of product information by... | Download Scientific Diagram
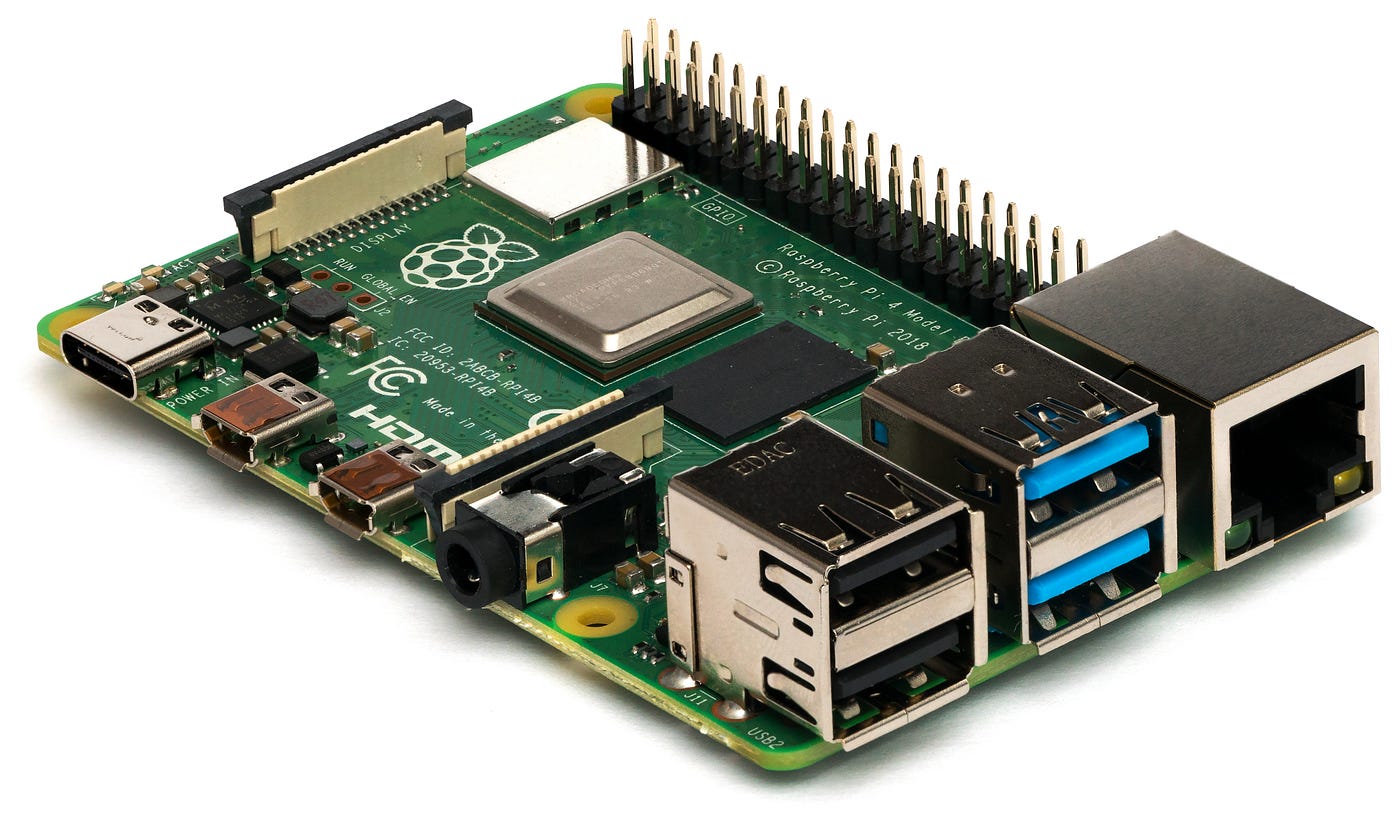
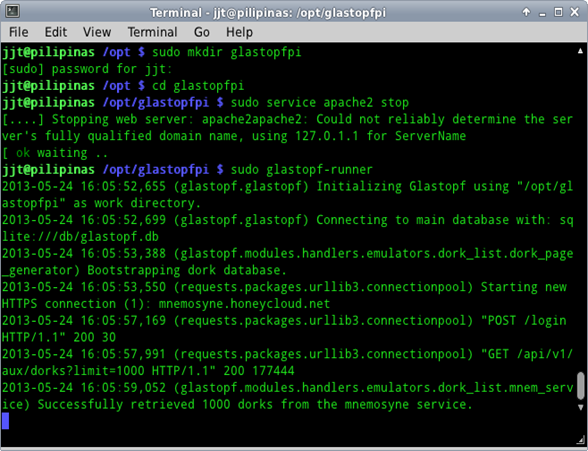
Step by Step Guide on setting up SMB, RDP, SSH and HTTP HoneyPot in Raspberry Pi | by Elaine Hung | Medium

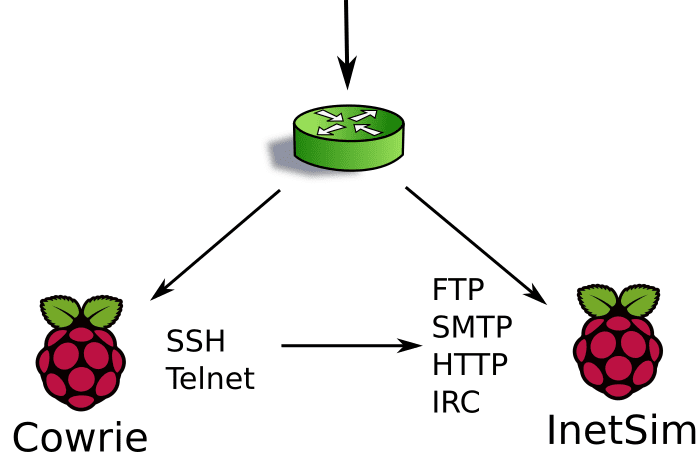
System architecture of our developed hardware IoT honeypot based on... | Download Scientific Diagram

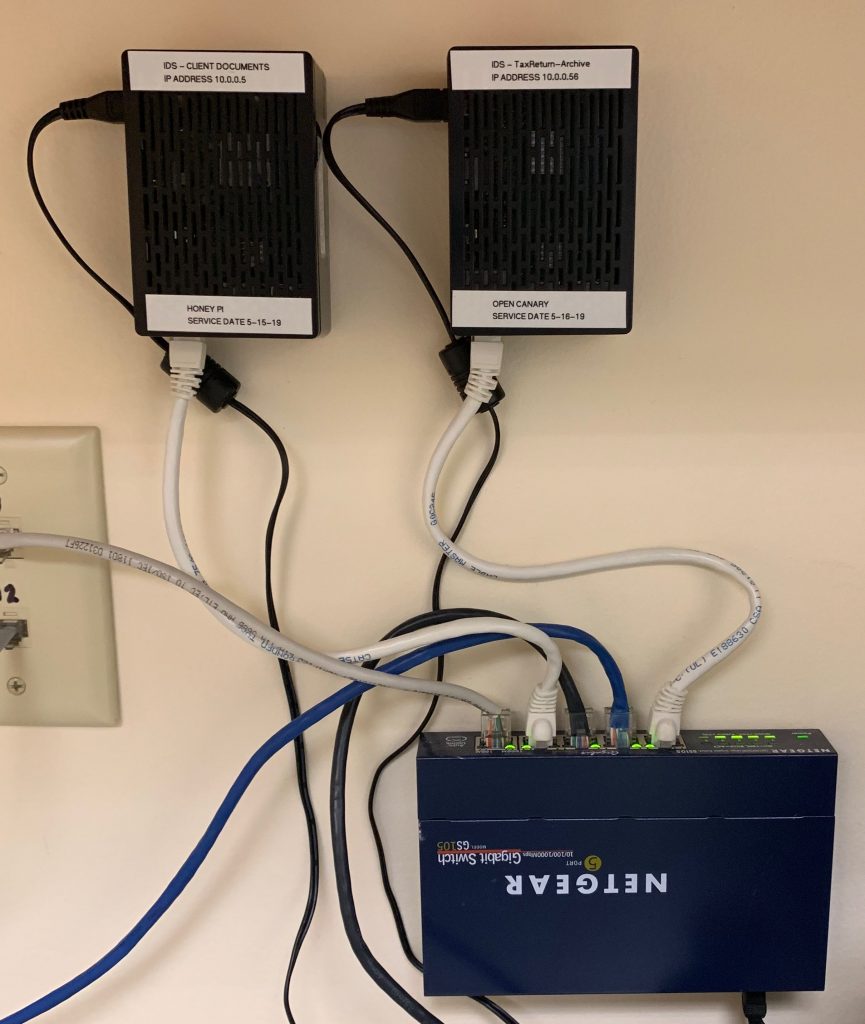
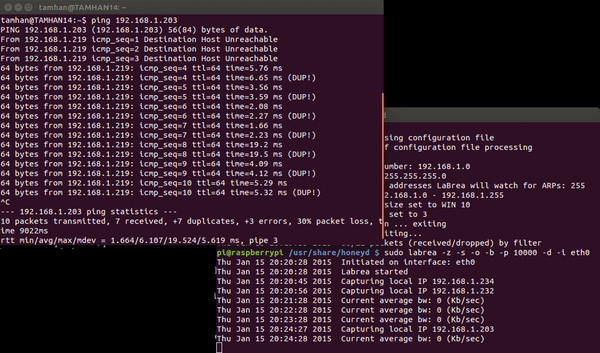
Build an easy RDP Honeypot with Raspberry PI 3 and observe the infamous attacks as (BlueKeep) CVE-2019–0708 : r/netsec